SAS® Management Console is by far my favourite SAS application. As a SAS platform administrator I like it because I can use it to administer much of the SAS 9 platform. I also like that I can use it to reach into, query and update SAS metadata in the SAS Metadata Server. My favourite interaction with SAS Management Console though is as a software developer and in this post I’ll explain why.
Way back in the mid 2000’s, when SAS 9.1.3 was the most recent version, I discovered SAS documentation for a SAS Management Console plug-in API and it spurred my imagination. Even with the best of applications there are always ways they can be improved, from one-off organization specific requirements to generic everyone-could-use-these features. The developers and designers of SAS Management Console, right from the early days with SAS 9.1, had planned for it to be extended with a documented API for adding custom functionality directly into the SAS application. I imagine this started from internal SAS requirements but I was very happy it made it into external documentation for us to use too. That was of course where Metacoda Plug-ins started. It’s amazing to think that I’ve been working with this application and it’s plug-in API for over 15 years.
What sort of things does the SAS Management Console plug-in API support? Continue reading “SAS Management Console: My Favourite SAS App”

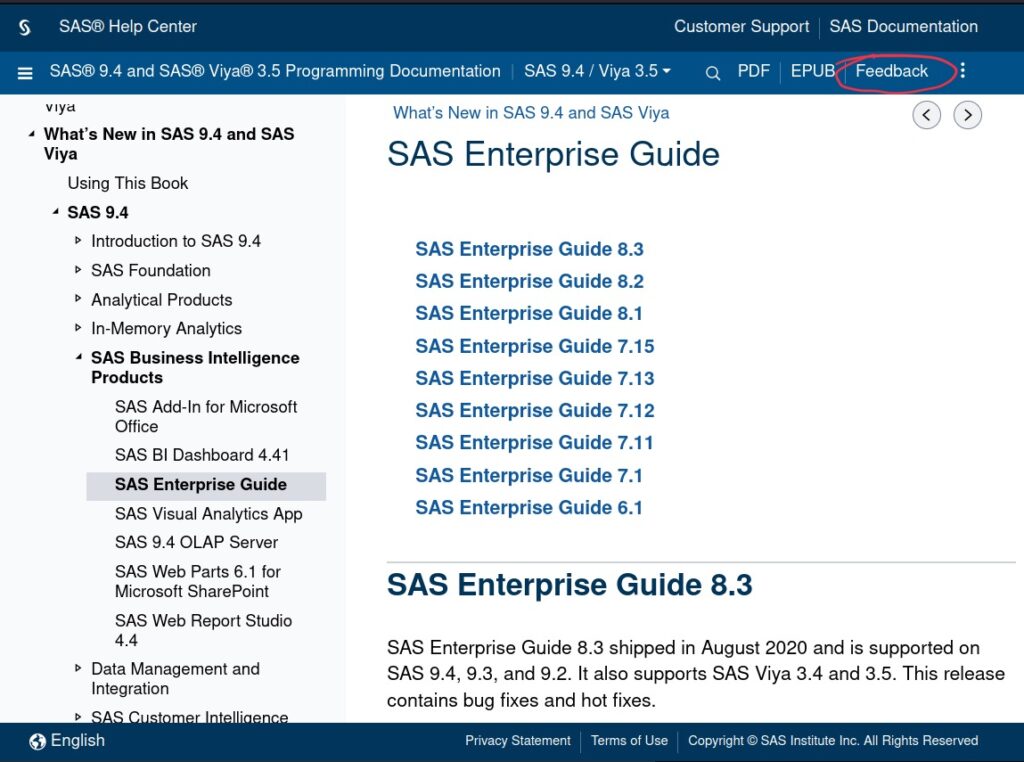
 Something I, and others, have been looking forward to for a while has been the release of SAS® 9.4 M8, and so I was excited to see Margaret Crevar’s SAS Communities post about it:
Something I, and others, have been looking forward to for a while has been the release of SAS® 9.4 M8, and so I was excited to see Margaret Crevar’s SAS Communities post about it: