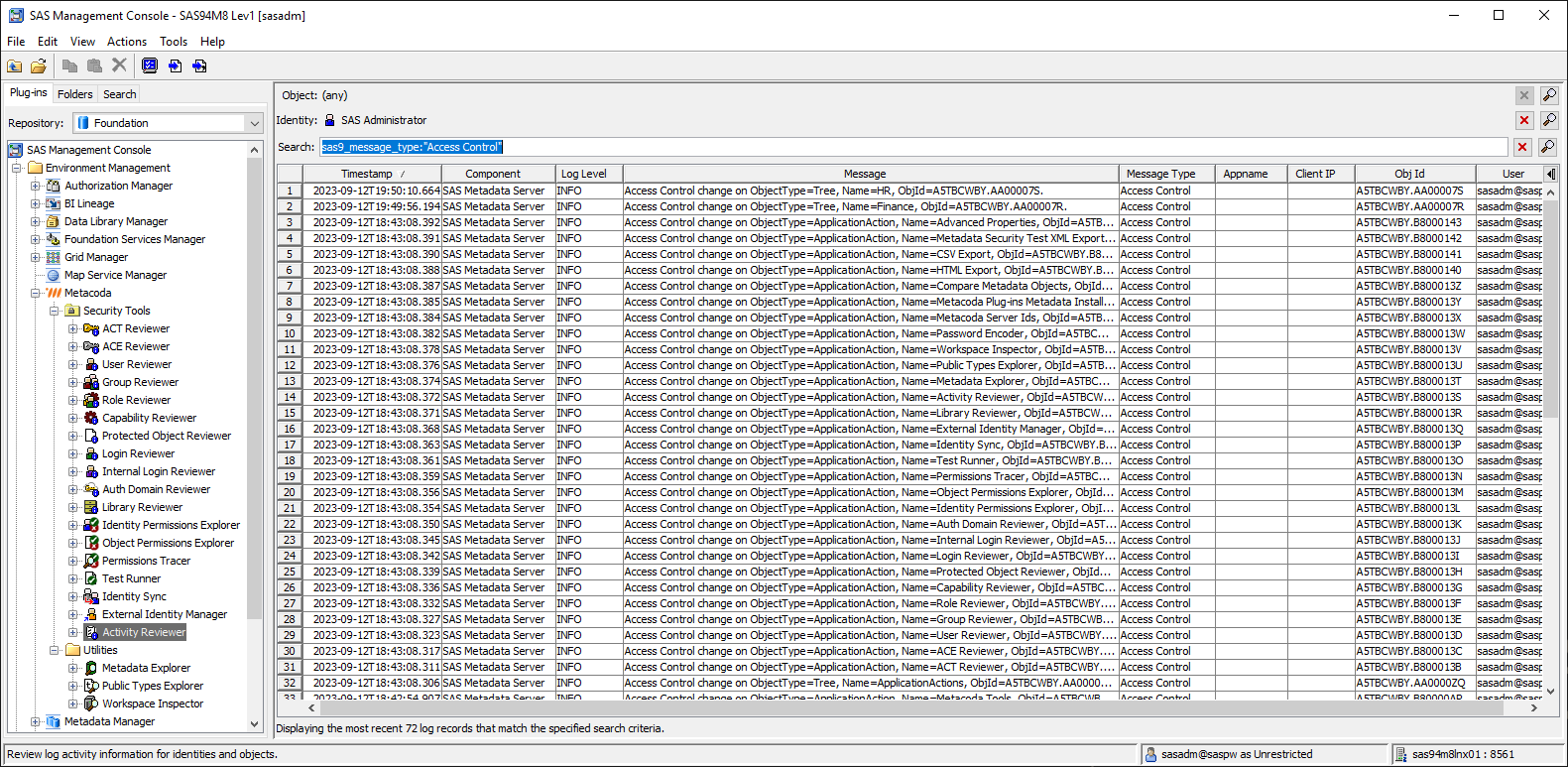
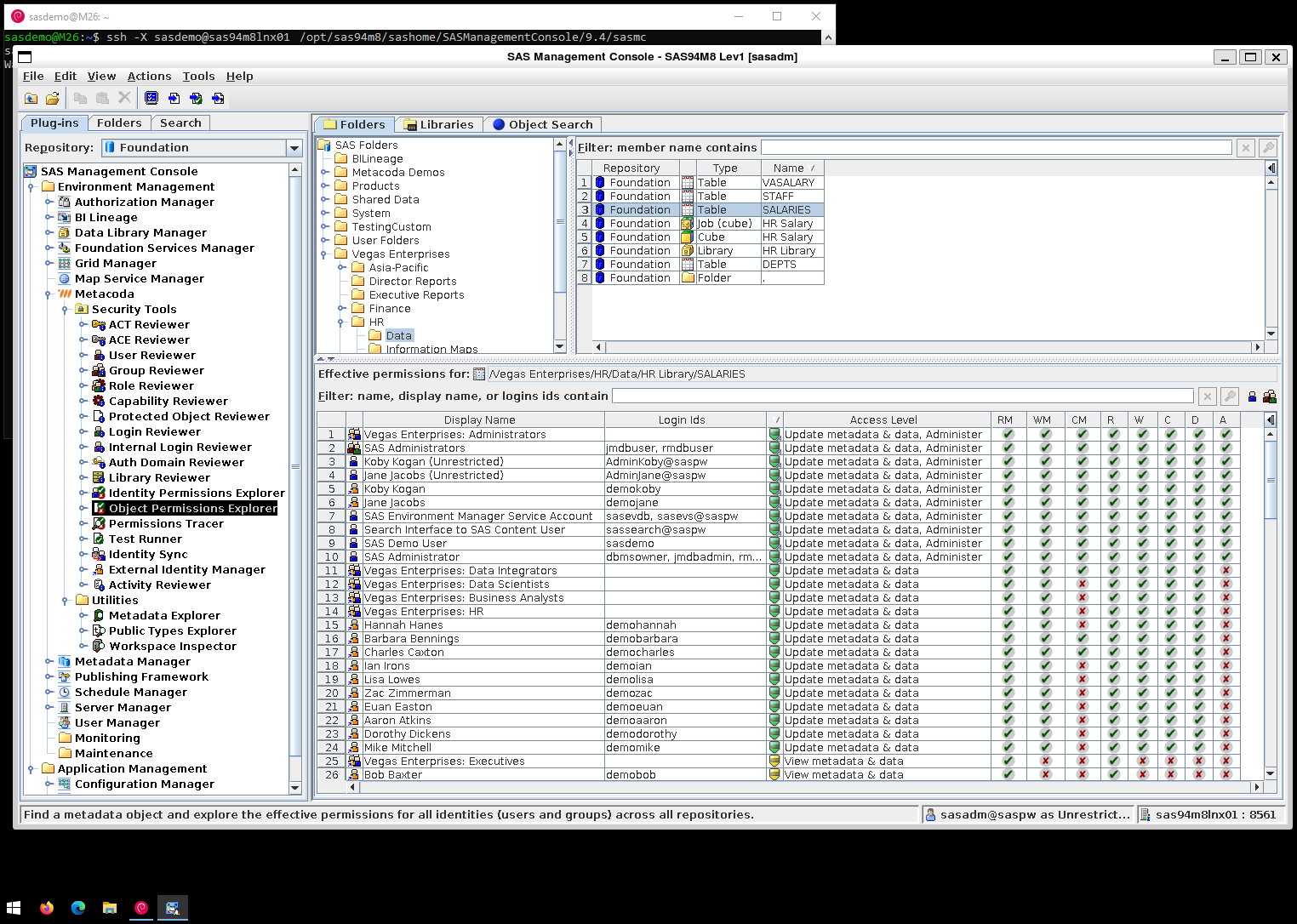
In my previous post on Finding Interesting SAS 9 Loggers, I highlighted 3 loggers I find useful for SAS 9 metadata access control change auditing, especially when using the new Metacoda Plug-ins 6.2 Activity Reviewer. There is also a 4th logger where you might already have trace level logging enabled, as it is configured so when you set up the SAS Environment Manager Service Architecture Audit, Performance, and Measurement (APM) component. In this post I want to go into more detail on each of those 4 loggers and explain what information they log and why I find them useful.
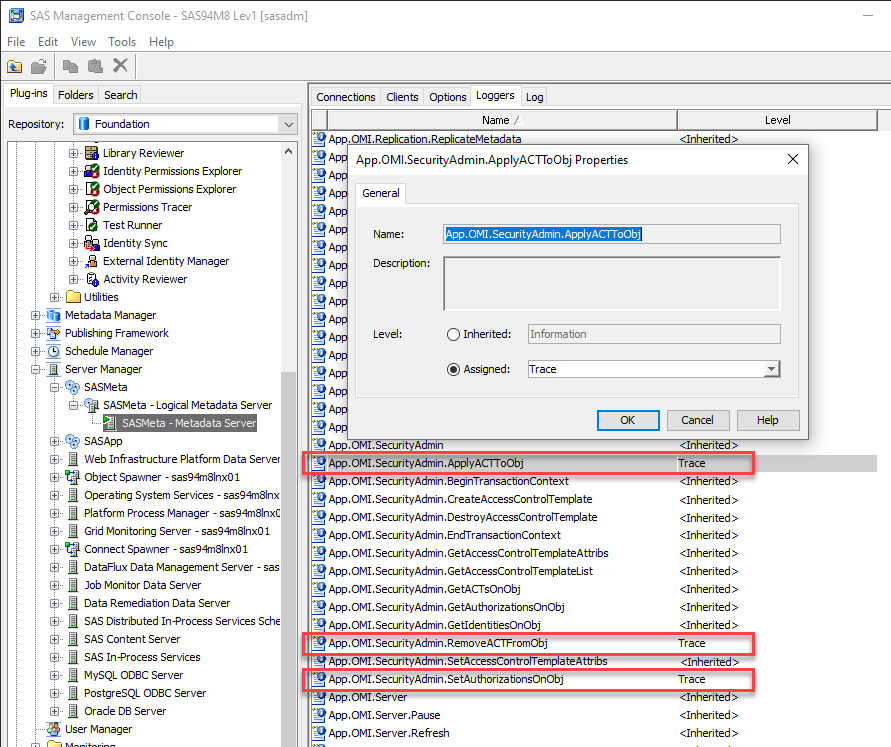
The loggers in question are:
- Audit.Meta.Security.AccCtrlAdm
- App.OMI.SecurityAdmin.SetAuthorizationsOnObj
- App.OMI.SecurityAdmin.ApplyACTToObj
- App.OMI.SecurityAdmin.RemoveACTFromObj
Continue reading “Interesting SAS 9 Metadata Server Access Control Loggers”