Chris Hemedinger’s new book Custom Tasks for SAS® Enterprise Guide® Using Microsoft .NET was recently released. If you have an idea for a really useful additional task you’d like to build for SAS Enterprise Guide, I strongly encourage you to read this book and find out how. I certainly got alot out of reading it and learning from Chris’ knowledge and experience.
I think I first spotted this book title about a year ago on SAS Publishing’s Upcoming Titles page. Since then I had been eagerly anticipating its release, so when it became available I was very keen to read it. I even got to provide a review for it too. You can read my review, along with several others, on the book’s reviews page.
One of the things I mentioned in my review was my desire to write a custom task to query SAS metadata from within SAS Enterprise Guide. After finishing the book, going through it a second time to pick up the bits I missed first time around :) , I then busily set about my .. hmm .. well .. ‘task’ …
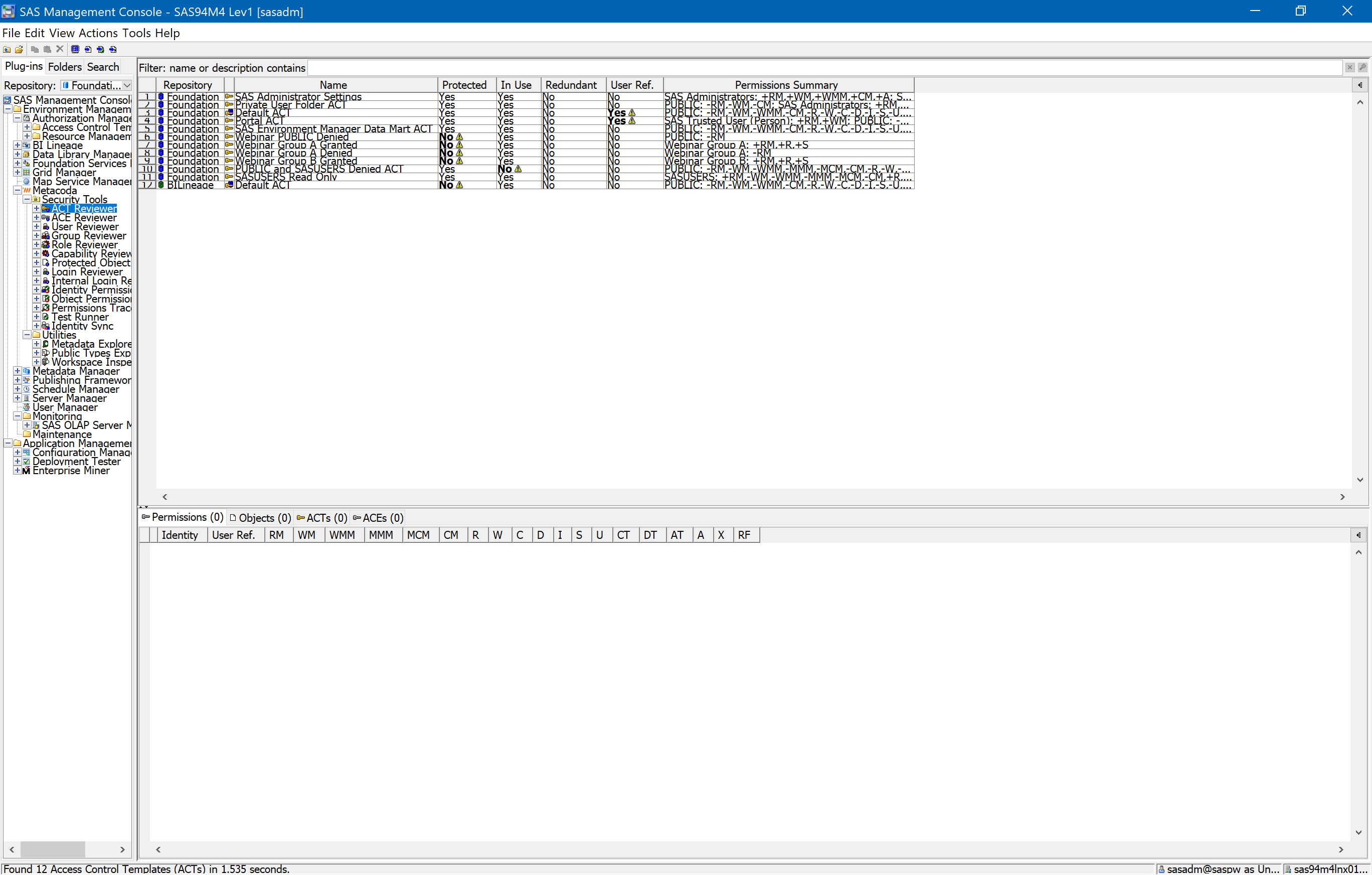
…. and then sometime later I had a working ‘Metadata Column Finder‘ task. Here’s a screenshot of it in action: Continue reading “Reading ‘Custom Tasks for SAS Enterprise Guide Using Microsoft .NET’”