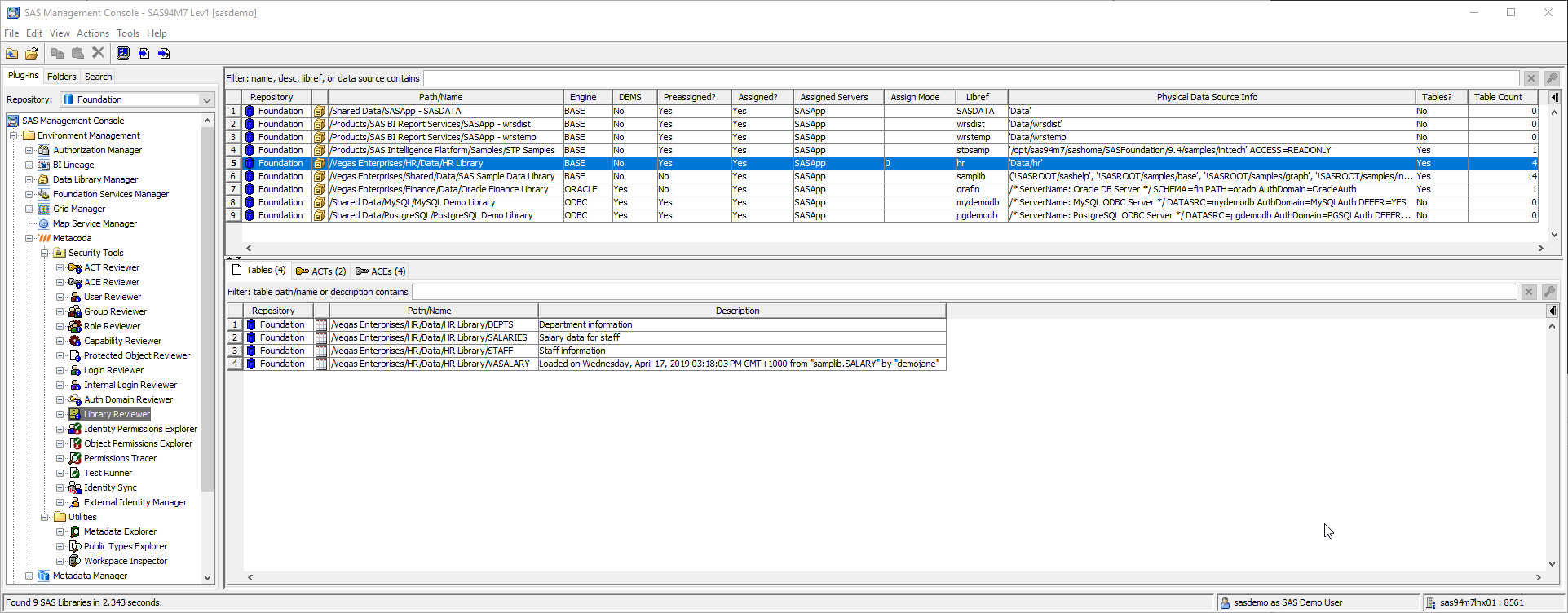
One of the most requested features from Metacoda customers has been a way to review all SAS® libraries registered in metadata, to see if they have been specifically protected with access controls, and to filter the list by various attributes like libref, engine, pre-assigned status, assigned server etc. Of course, to also be able to export to CSV and HTML as with the other plug-ins. The recent Metacoda Plug-ins 6.1 R8 release adds a new Library Reviewer plug-in to assist with this.
The list of libraries is presented at the top of the screen and selecting a library will Continue reading “Metacoda Plug-ins: Library Reviewer”