Update 05Mar2019: The Metadata Auth Domain Reviewer discussed in this blog post is now available with the Metacoda Plug-ins 6.1 R1 release, and also includes a new Libraries tab based on feedback from customers during early-access testing.
One of the new Metacoda Security Plug-ins features arriving in version 6.1 is the Auth Domain Reviewer. Like the other reviewers, this plug-in is used for investigating, documenting and testing how a SAS metadata security feature has been used within a particular SAS platform deployment. When I’m reviewing metadata security for a SAS platform I like to look at it from several different perspectives and authentication domains is one of them. I like to see:
- What authentication domains have been added beyond the initial DefaultAuth?
- How have they been used with respect to inbound logins?
- How have they been used with respect to outbound logins and providing shared credentials for database access?
- How have they been used with respect to 3rd party database system connections?
- Are there any unused ones, possibly added by accident, that can be cleaned up?
- Are there any seemingly duplicate ones that might be consolidated?
In the past it has been time-consuming to gather this information together, so this new plug-in is a welcome addition allowing us to answer those types of questions faster and more easily.
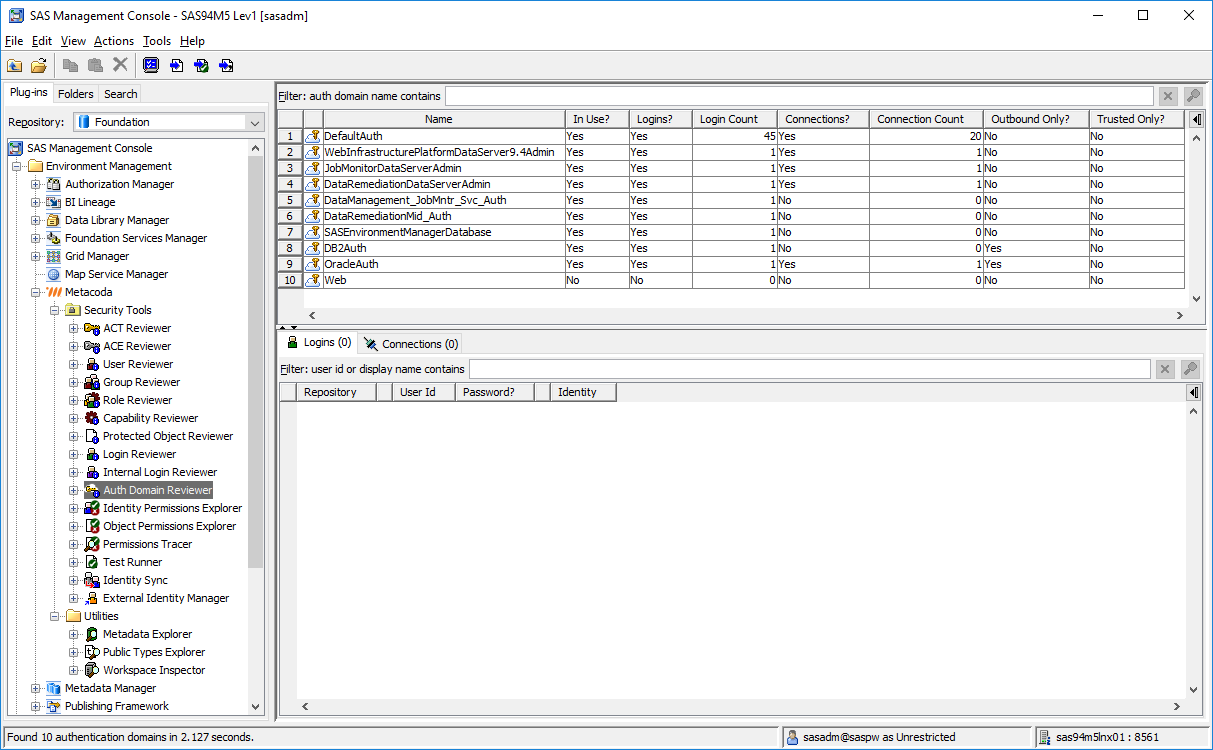
Looking at this initial screenshot, showing the Auth Domain Reviewer plug-in selected within SAS Management Console 9.4, we can see an overview of the authentication domains present in this (demo) environment:
There are several things that immediately stand out from this overview:
- There are 10 auth domains present.
- Most of the logins are in the DefautAuth domain, as you might expect.
- All but one of the auth domains (Web) have associated logins.
- Two of the auth domains have been tagged as outbound-only (DB2Auth and OracleAuth).
- None of the auth domains have been tagged as trusted-only.
- Some of the auth domains have no associated server connections, mostly being domains pre-installed during SAS deployment, and ones we will leave alone (DataManagement_JobMntr_Svc_Auth, DataRemediationMid_Auth, and SASEnvironmentManagerDatabase)
- Whilst the DB2Auth domain has an associated login it has no associated server connections. How is this login being used and is it still required is a question to be asked.
- The Web auth domain appears unused, having no associated logins and no associated server connections. Perhaps it comes from an aborted trusted web authentication configuration and can be removed, or is going to be used in a future trusted web authentication configuration. Certainly another question to be followed up.
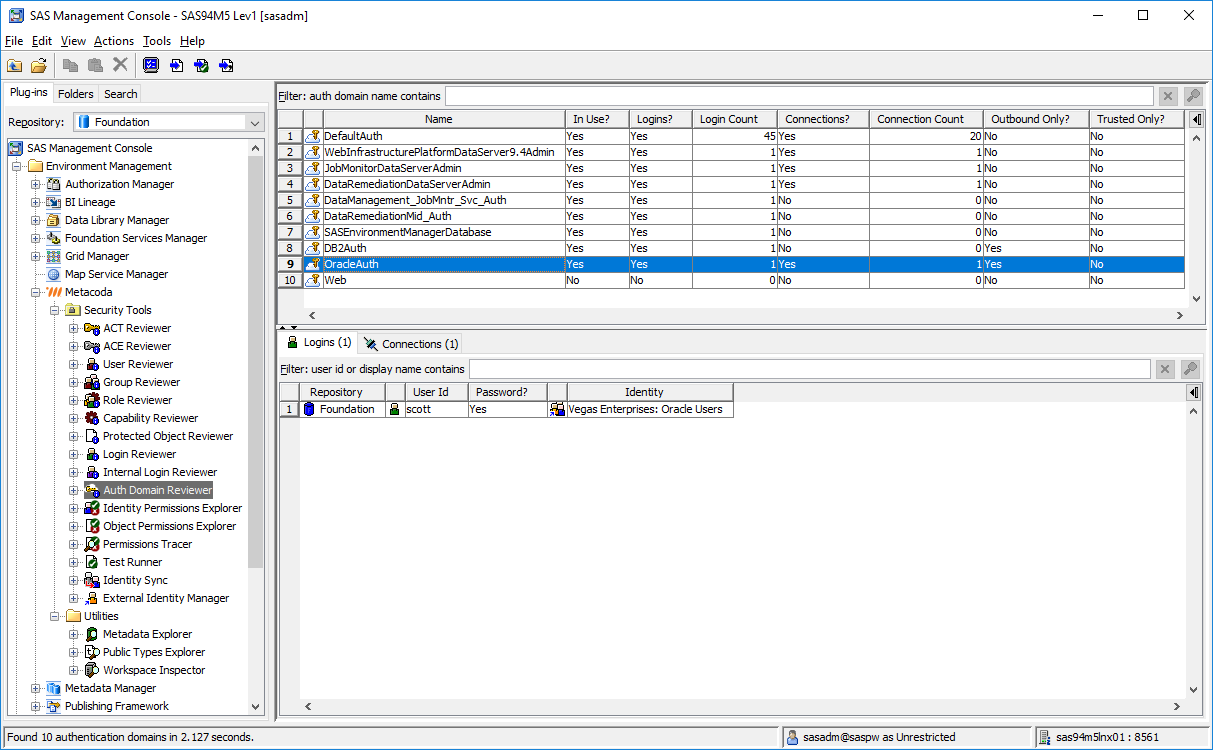
The next screenshot shows the Logins tab with the OracleAuth domain selected:
It shows the OracleAuth domain has one associated login, shared via the Vegas Enterprises: Oracle Users group, with a user id of scott and a password stored in metadata.
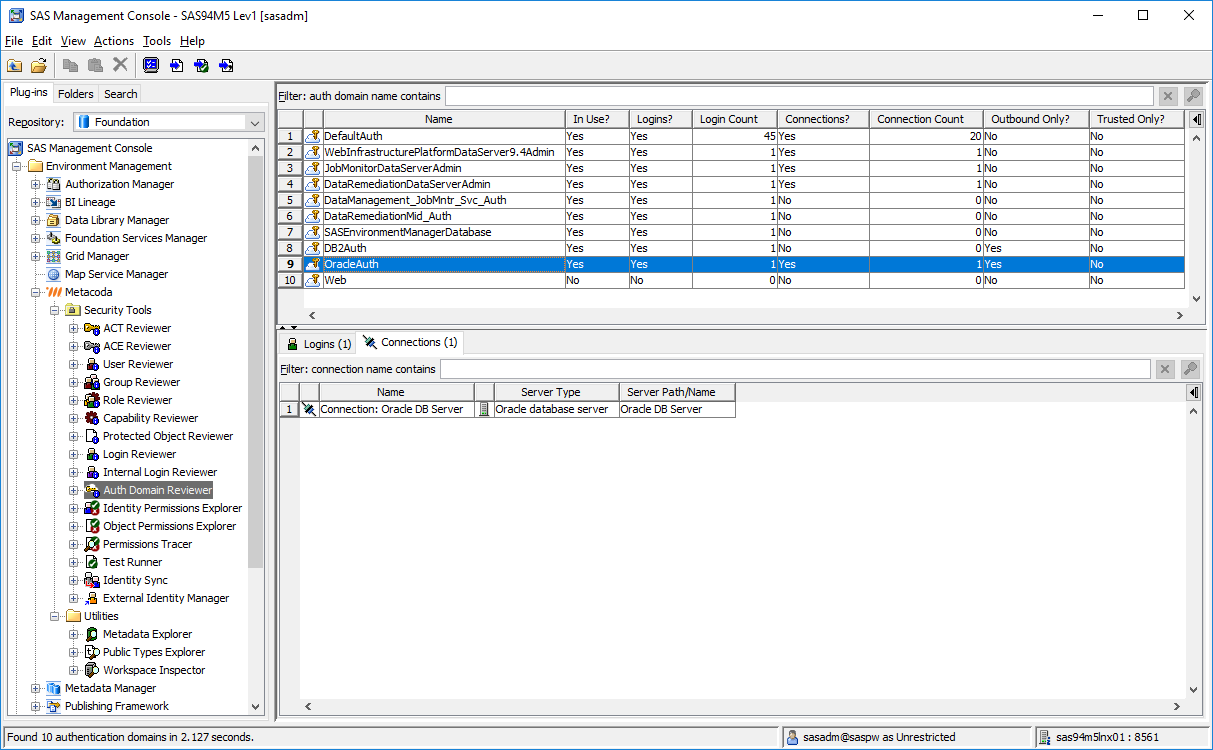
This next screenshot shows the Connections tab for same selected OracleAuth domain:
It shows the OracleAuth domain has one associated server connection (Connection: Oracle DB Server) for the Oracle DB Server. You would find that server and connection with the standard SAS Management Console Server Manager plug-in.
For documentation purposes, you can export a HTML report of all of this auth domain information. You could also export a CSV file summarizing the list of auth domains. If you want to go further and export a Metadata Security Test XML file, you can use it as the basis of ongoing automated/scheduled testing of the use of authentication domains in the environment. As an example, the following test fragment can be used to ensure security tests will fail, and we will get an email alert, if someone tampers with the OracleAuth domain in an unexpected way (removed, renamed, scott login removed/modified, associated database connection removed etc).:
<SecTest ... >
...
<AuthDomains>
...
<AuthDomain required="true" name="OracleAuth" desc="" outboundOnly="true" trustedOnly="false">
<Logins complete="true">
<Login required="true" userId="scott" hasPassword="true" />
</Logins>
<Connections complete="true">
<Connection required="true" name="Connection: Oracle DB Server"/>
</Connections>
</AuthDomain>
...
</AuthDomains>
</SecTest>If you would like to try out this new Auth Domain Reviewer plug-in, a beta version of Metacoda Plug-ins 6.1 is now available for testing. Contact me or Metacoda if you would like to get access to the beta. Metacoda customers can use their existing Metacoda Plug-ins 6.0 license with 6.1 and we can provide a free short-term evaluation license for any other SAS customers who would also like to test it out.
The eagle-eyed may have noticed another new plug-in from the 6.1 screenshots above: that’s the External Identity Manager and used to help efficiently manage/manipulate external identity metadata for identities synchronised with Active Directory / LDAP – it’ll be of interest to those who use the Metacoda Identity Sync plug-in, or custom code using the SAS %MDU macros. External Identity Manager is going to be the subject of future blog posts but, if you’d like to try that out, it’s also available in the 6.1 beta.

Thank you for this new plugin, long awaited :)
Really, great news!
Thanks Juan! Let me know if you’d like to try it out.